As most of you have probably been doing, I have been reading with interest and quite considerable amounts of concern (not that I have anything to hide) about the top secret American surveillance program called PRISM which has been in the press for the last few days.
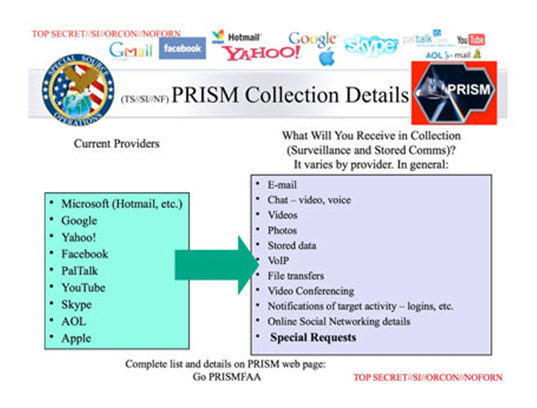
For those of you that have not been reading or heard anything about it this is a program that allows the National Security Agency (NSA) direct access into the systems of such internet giants as Google, Facebook, Apple, Microsoft and many, many more.
This access allows the operating agency to collect details of users search history, email content, file transfers, live chats, and much, much more.
This has all come to light as The Guardian newspaper came into possession of, and authenticated, a 41 page Top Secret document that was not even to be distributed to foreign allies. This document was apparently used to train US intelligence operatives on what the system was capable of including “collection directly from the servers” of major US service providers
The same presentation states that the program is run with the assistance of the companies concerned however any knowledge of such a program has been denied so far.
Both Google and Microsoft publicly repeatedly voice their concern about protecting their customers data however all of the major internet and computer ‘players’ have been rumoured to sell a lot of this information to advertisers in the past so I for one am a little confused and sceptical.
The top secret document contains the below chart which appears to have been prepared by the NSA that shows what information is obtainable by this system and which providers this information is available from.
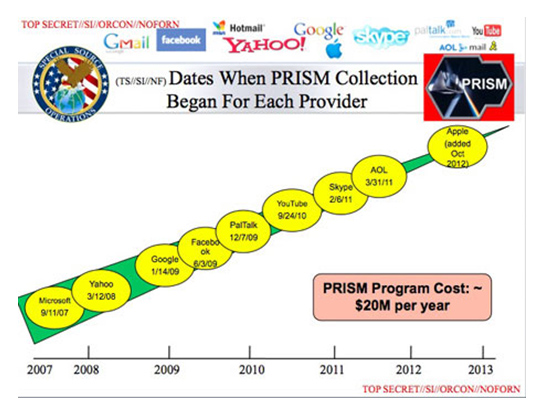
And the following chart, also from the document, shows how long this appears to have been going on.
The document is dated up to April 2013 and could prove to be rather embarrassing for the publisher, the NSA, who usually prides itself on its high level of secrecy.
The document is believed to have been ‘leaked’ by 29 year old NSA contract analyst Edward J Snowden who is currently in Hong Kong where he feels he is safest from the control of the US Government?
At spycatcheronline we are currently working on software to protect your emails and text messages and currently have two options for cellular telephone encryption.
Both of these are point to point scramblers which mean that both people involved in the telephone conversation have to have one so that every part of the call is protected and there is no weak point where interception and comprehension could take place.
Jane Bond
Facts from The Guardian Online